Result pattern vs Exceptions - The Battle for clean .NET APIs
- When building APIs in .NET, one common design debate is
- 𝗦𝗵𝗼𝘂𝗹𝗱 𝗜 𝗿𝗲𝘁𝘂𝗿𝗻 𝗮 𝗥𝗲𝘀𝘂𝗹𝘁<𝗧> 𝗼𝗿 𝘁𝗵𝗿𝗼𝘄 𝗲𝘅𝗰𝗲𝗽𝘁𝗶𝗼𝗻𝘀 𝘄𝗵𝗲𝗻 𝘀𝗼𝗺𝗲𝘁𝗵𝗶𝗻𝗴 𝗴𝗼𝗲𝘀 𝘄𝗿𝗼𝗻𝗴?
- After working with both approaches across various projects, here's a practical comparison to help you decide what works best for your architecture.
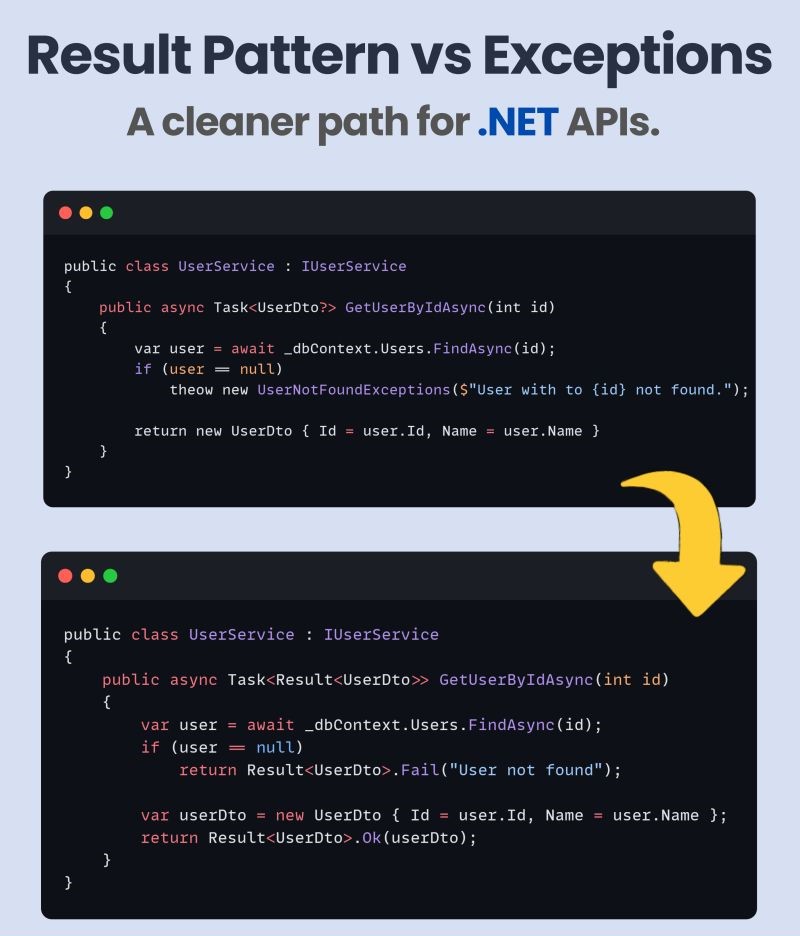
𝗧𝗵𝗲 𝗦𝗰𝗲𝗻𝗮𝗿𝗶𝗼
- Let’s say you're fetching a user by ID. If the user doesn't exist, do you:
- Throw a UserNotFoundException?
- Return a structured Result
with a failure message? - Both approaches are valid, but they solve different problems.
𝗧𝗵𝗲 𝗖𝗮𝘀𝗲 𝗳𝗼𝗿 𝗥𝗲𝘀𝘂𝗹𝘁<𝗧>
- The Result
pattern wraps success/failure states in a single object. It’s predictable, consistent, and ideal for business logic outcomes. - Why developers love it:
- Clear separation of success and failure
- No exception overhead
- Consistent response shape for clients
- Easier to test (no try-catch needed)
𝐒𝐡𝐨𝐫𝐭-𝐜𝐢𝐫𝐜𝐮𝐢𝐭 𝐩𝐚𝐭𝐭𝐞𝐫𝐧
- Sometimes you intentionally stop the pipeline early
- Common for health checks and lightweight endpoints
𝗧𝗵𝗲 𝗖𝗮𝘀𝗲 𝗳𝗼𝗿 𝗘𝘅𝗰𝗲𝗽𝘁𝗶𝗼𝗻𝘀
- Throwing exceptions is useful for signaling unexpected failures, like DB connection issues or null references.
- Why exceptions still make sense:
- Cleaner service code (no if checks)
- Built-in middleware support in .NET
- Better suited for truly exceptional cases
𝗠𝘆 𝗥𝘂𝗹𝗲 𝗼𝗳 𝗧𝗵𝘂𝗺𝗯:
- Use Result
for expected, business-level outcomes. - Use exceptions for unexpected, system-level issues.
𝐂𝐎𝐑𝐒 𝐦𝐢𝐝𝐝𝐥𝐞𝐰𝐚𝐫𝐞
- CORS must run after routing and before authentication
- Use named policies for clean control (per app / per endpoint)
𝐀𝐮𝐭𝐡𝐞𝐧𝐭𝐢𝐜𝐚𝐭𝐢𝐨𝐧 → 𝐀𝐮𝐭𝐡𝐨𝐫𝐢𝐳𝐚𝐭𝐢𝐨𝐧
- Authentication identifies who the user is
- Authorization decides what the user is allowed to do
- The order is critical for correct security behavior
𝐑𝐚𝐭𝐞 𝐥𝐢𝐦𝐢𝐭𝐢𝐧𝐠
- Rate limiting protects APIs from abuse and traffic spikes.
- It can be applied globally or per endpoint and returns 429 when limits are exceeded
𝐂𝐨𝐦𝐩𝐫𝐞𝐬𝐬𝐢𝐨𝐧 & 𝐜𝐚𝐜𝐡𝐢𝐧𝐠
- Response compression can significantly reduce payload size
- Caching avoids unnecessary recomputation
- Compression should run before caching, and caching should be limited to safe requests
𝐂𝐮𝐬𝐭𝐨𝐦 𝐦𝐢𝐝𝐝𝐥𝐞𝐰𝐚𝐫𝐞
- When built-in middleware is not enough:
- request/response logging, tenant resolution, correlation IDs, feature flags, and custom guards all fit here
- Middleware in .NET Applications often looks simple until it is not
- Mastering order and responsibility is one of the fastest ways to level up as an ASP.NET Core developer